Nextcloud Client Wont Connect Error Reads Ldap Server
User authentication with LDAP
Nextcloud ships with an LDAP application to allow LDAP users (including Active Directory) to appear in your Nextcloud user listings. These users will authenticate to Nextcloud with their LDAP credentials, so you don't accept to create split Nextcloud user accounts for them. Yous will manage their Nextcloud group memberships, quotas, and sharing permissions merely like whatsoever other Nextcloud user.
Notation
The PHP LDAP module is required; this is supplied by php-ldap on near distributions.
The LDAP application supports:
-
LDAP grouping back up
-
File sharing with Nextcloud users and groups
-
Access via WebDAV and Nextcloud Desktop Client
-
Versioning, external Storage and all other Nextcloud features
-
Seamless connectivity to Agile Directory, with no extra configuration required
-
Support for primary groups in Active Directory
-
Auto-detection of LDAP attributes such every bit base DN, email, and the LDAP server port number
-
Only read access to your LDAP (edit or delete of users on your LDAP is not supported)
-
Optional: Allow users to change their LDAP password from Nextcloud
Note
A not-blocking or correctly configured SELinux setup is needed for the LDAP backend to work. Delight refer to the SELinux configuration.
Configuration
First enable the LDAP user and group backend app on the Apps page in Nextcloud. Then go to your Admin folio to configure information technology.
The LDAP configuration console has four tabs. A correctly completed commencement tab ("Server") is mandatory to admission the other tabs. A green indicator lights when the configuration is correct. Hover your cursor over the fields to come across some popular-upwards tooltips.
Server tab
Start with the Server tab. Y'all may configure multiple servers if you have them.
Annotation
Do not configure any failover LDAP hosts hither. See Advanced settings for instructions instead.
At a minimum yous must supply the LDAP server'southward hostname. If your server requires authentication, enter your credentials on this tab. Nextcloud will then endeavor to auto-find the server'due south port and base DN. The base DN and port are mandatory, then if Nextcloud cannot notice them you must enter them manually.
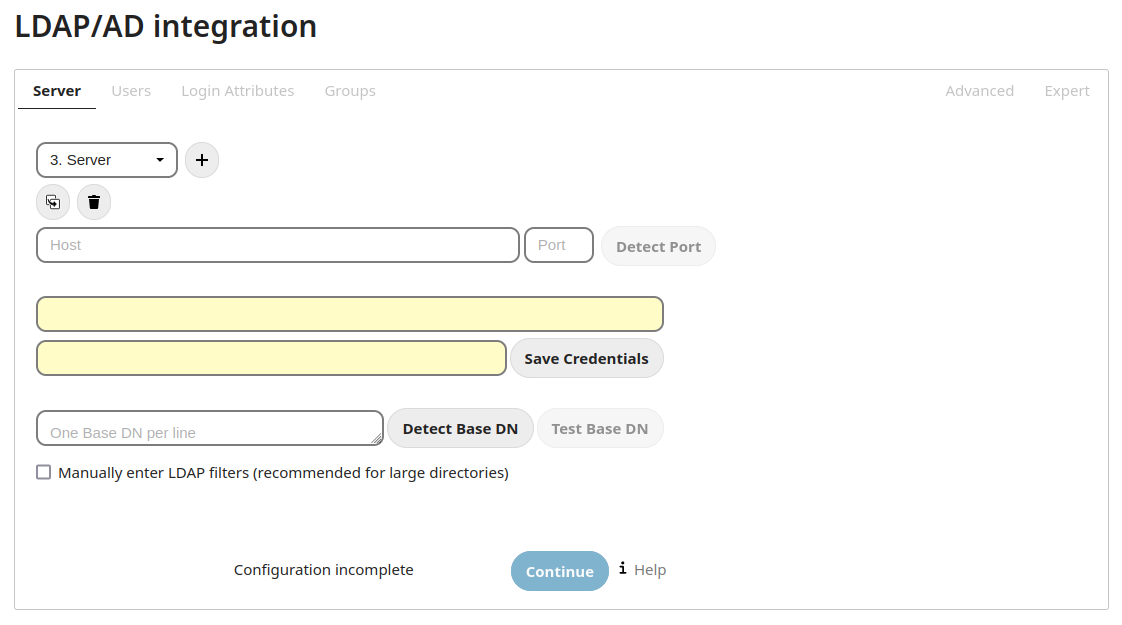
- Server configuration:
-
Configure one or more LDAP servers. Click the Delete Configuration button to remove the active configuration.
- Host:
-
The host proper name or IP address of the LDAP server. It tin can also be a ldaps:// URI. If you enter the port number, it speeds up server detection.
Examples:
-
directory.my-company.com
-
ldaps://directory.my-company.com
-
directory.my-company.com:9876
-
- Port:
-
The port on which to connect to the LDAP server. The field is disabled in the beginning of a new configuration. If the LDAP server is running on a standard port, the port will be detected automatically. If you are using a non-standard port, Nextcloud volition attempt to detect information technology. If this fails you must enter the port number manually.
Example:
-
389
-
- User DN:
-
The proper noun every bit DN of a user who has permissions to do searches in the LDAP directory. Leave it empty for anonymous access. We recommend that you have a special LDAP organization user for this.
Example:
-
uid=nextcloudsystemuser,cn=sysusers,dc=my-company,dc=com
-
- Countersign:
-
The password for the user given above. Empty for anonymous admission.
- Base DN:
-
The base DN of LDAP, from where all users and groups can be reached. Y'all may enter multiple base DNs, one per line. (Base DNs for users and groups can be fix in the Advanced tab.) This field is mandatory. Nextcloud attempts to determine the Base DN according to the provided User DN or the provided Host, and you must enter it manually if Nextcloud does not find it.
Example:
-
dc=my-company,dc=com
-
Users tab
Utilize this to control which LDAP users are listed as Nextcloud users on your Nextcloud server. In order to command which LDAP users tin can login to your Nextcloud server use the Login Attributes tab. Those LDAP users who have access merely are not listed as users (if at that place are any) will exist subconscious users. You lot may bypass the form fields and enter a raw LDAP filter if you prefer.
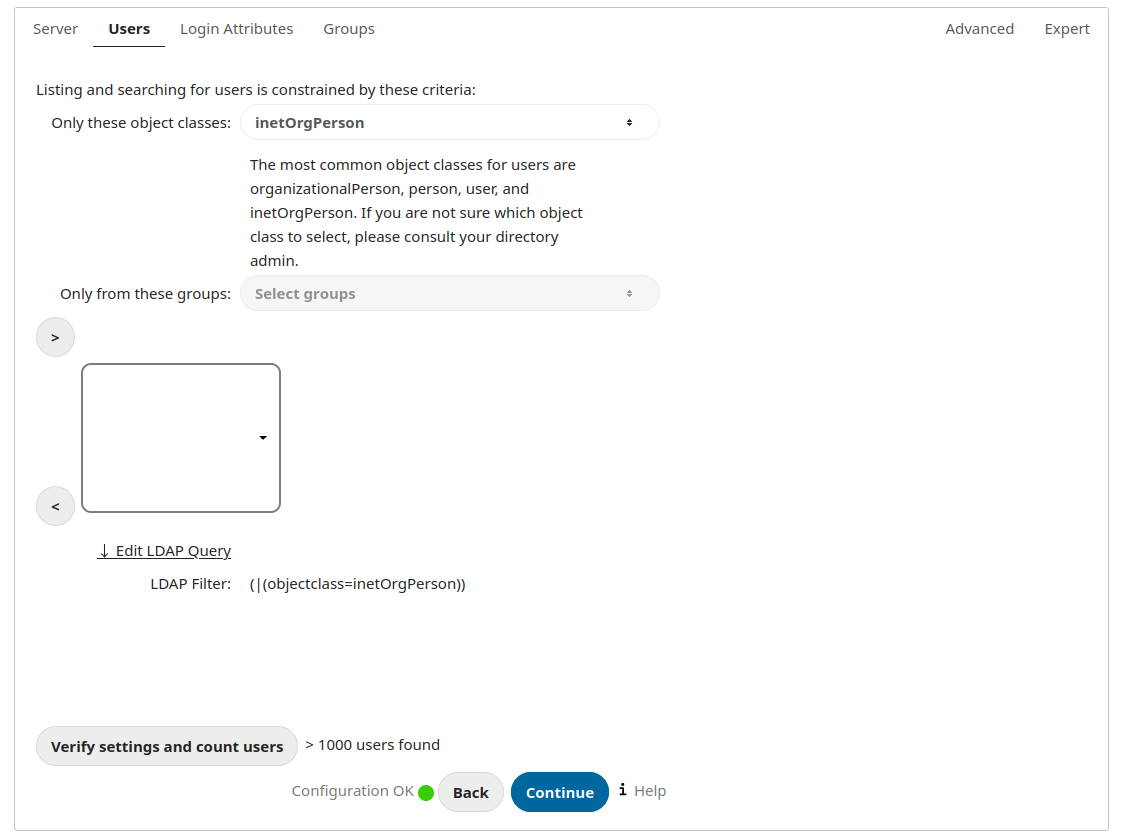
- Merely those object classes:
-
Nextcloud will determine the object classes that are typically available for user objects in your LDAP. Nextcloud volition automatically select the object course that returns the highest amount of users. Y'all may select multiple object classes.
- Only from those groups:
-
If your LDAP server supports the
fellow member-of-overlayin LDAP filters, yous tin can define that only users from one or more than certain groups are allowed to appear in user listings in Nextcloud. By default, no value will exist selected. You may select multiple groups.If your LDAP server does non support the
member-of-overlayin LDAP filters, the input field is disabled. Delight contact your LDAP administrator. - Edit LDAP Query:
-
Clicking on this text toggles the filter mode and you can enter the raw LDAP filter direct. Case:
( & ( objectClass = inetOrgPerson )( memberOf = cn = nextcloudusers , ou = groups , dc = example , dc = com ))
- x users found:
-
This is an indicator that tells you approximately how many users will be listed in Nextcloud. The number updates automatically after any changes.
Login attributes tab
The settings in the Login Attributes tab decide which LDAP users tin can log in to your Nextcloud organisation and which attribute or attributes the provided login name is matched against (due east.yard. LDAP/Advertisement username, email address). Y'all may select multiple user details. (You may featherbed the grade fields and enter a raw LDAP filter if you prefer.)
You may override your User Filter settings on the Users tab by using a raw LDAP filter.
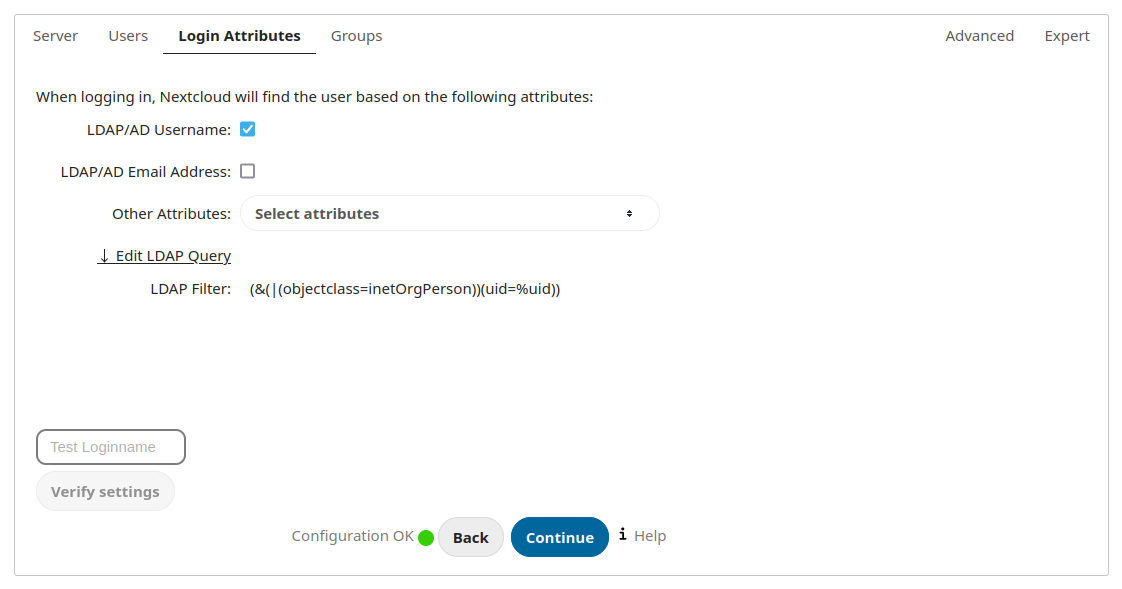
- LDAP Username:
-
If this value is checked, the login value will exist compared to the username in the LDAP directory. The corresponding attribute, usually uid or samaccountname will be detected automatically by Nextcloud.
- LDAP Email Accost:
-
If this value is checked, the login value volition be compared to an email accost in the LDAP directory; specifically, the mailPrimaryAddress and mail attributes.
- Other Attributes:
-
This multi-select box allows you to select other attributes for the comparing. The listing is generated automatically from the user object attributes in your LDAP server.
- Edit LDAP Query:
-
Clicking on this text toggles the filter mode and you tin enter the raw LDAP filter directly.
The %uid placeholder is replaced with the login proper name entered by the user upon login.
Examples:
-
only username:
( & ( objectClass = inetOrgPerson )( memberOf = cn = nextcloudusers , ou = groups , dc = instance , dc = com )( uid =% uid )
-
username or electronic mail address:
(( & ( objectClass = inetOrgPerson )( memberOf = cn = nextcloudusers , ou = groups , dc = example , dc = com )( | ( uid =% uid )( postal service =% uid )))
-
Groups tab
By default, no LDAP groups will be available in Nextcloud. The settings in the Groups tab decide which groups volition be available in Nextcloud. You may also elect to enter a raw LDAP filter instead.
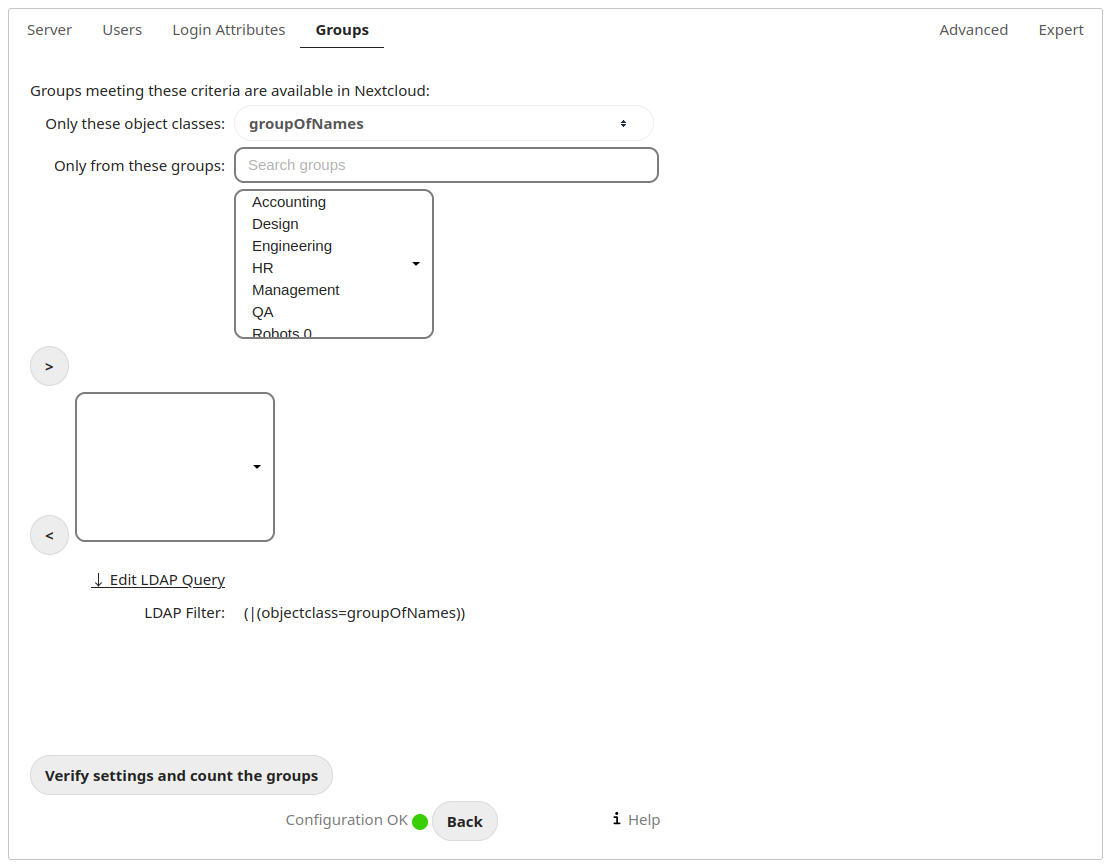
- Only these object classes:
-
Nextcloud will determine the object classes that are typically available for group objects in your LDAP server. Nextcloud volition only list object classes that return at least one group object. You can select multiple object classes. A typical object class is "group", or "posixGroup".
- But from these groups:
-
Nextcloud volition generate a list of bachelor groups found in your LDAP server. And so you select the group or groups that become access to your Nextcloud server.
- Edit LDAP Query:
-
Clicking on this text toggles the filter fashion and you lot tin can enter the raw LDAP filter directly.
Example:
-
objectClass=grouping
-
objectClass=posixGroup
-
- y groups found:
-
This tells y'all approximately how many groups will be bachelor in Nextcloud. The number updates automatically later any change.
Advanced settings
The LDAP Advanced Setting section contains options that are not needed for a working connection. This provides controls to disable the current configuration, configure replica hosts, and various functioning-enhancing options.
The Advanced Settings are structured into three parts:
-
Connection Settings
-
Directory Settings
-
Special Attributes
Connection settings
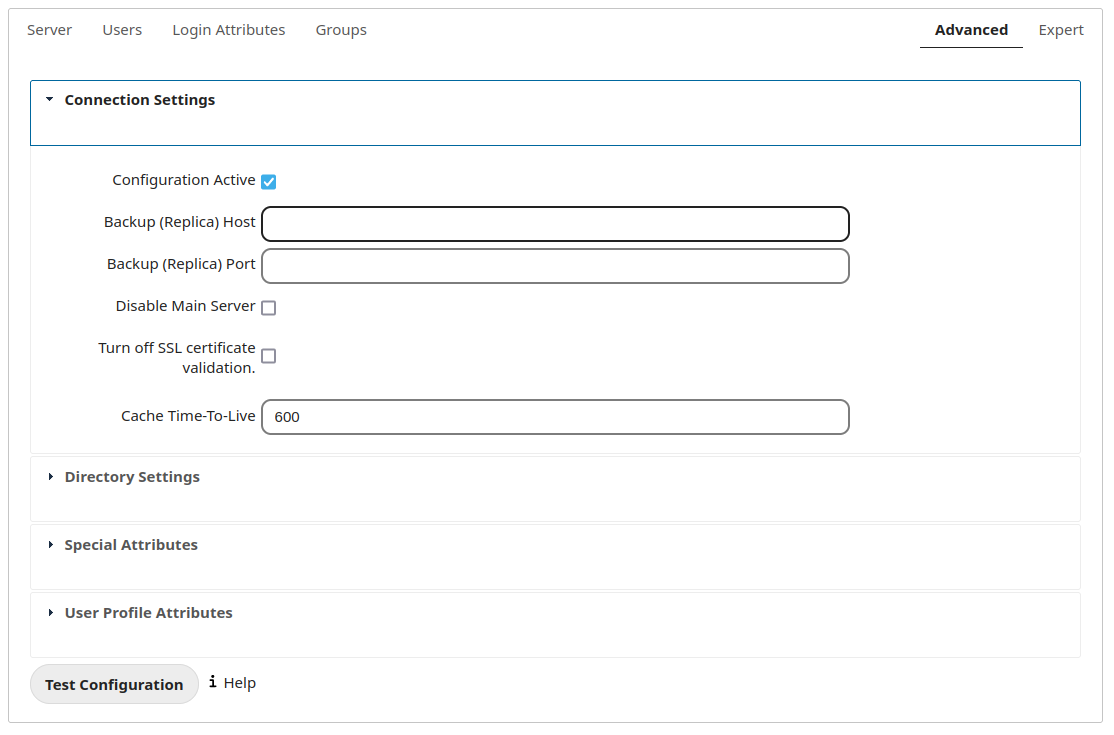
- Configuration Active:
-
Enables or Disables the current configuration. Past default, it is turned off. When Nextcloud makes a successful test connection information technology is automatically turned on.
- Backup (Replica) Host:
-
If you have a fill-in LDAP server, enter the connection settings here. Nextcloud volition then automatically connect to the backup when the main server cannot be reached. The backup server must be a replica of the principal server and so that the object UUIDs match.
Example:
-
directory2.my-company.com
-
- Backup (Replica) Port:
-
The connection port of the backup LDAP server. If no port is given, merely merely a host, then the master port (as specified above) volition be used.
Example:
-
389
-
- Disable Main Server:
-
Yous can manually override the main server and make Nextcloud only connect to the backup server. This is useful for planned downtimes.
- Plough off SSL certificate validation:
-
Turns off SSL certificate checking. Use it for testing only! Annotation: The event of this setting depends on the PHP system configuration. It does for case not work with the [official Nextcloud container image](https://github.com/nextcloud/docker). To disable certificate verification for a item apply, append the following configuration line to your /etc/ldap/ldap.conf:
` TLS_REQCERT Permit ` - Enshroud Time-To-Alive:
-
A enshroud is introduced to avoid unnecessary LDAP traffic, for instance caching usernames so they don't have to be looked up for every page, and speeding up loading of the Users page. Saving the configuration empties the enshroud. The time is given in seconds.
Note that well-nigh every PHP asking requires a new connectedness to the LDAP server. If yous require fresh PHP requests we recommend defining a minimum lifetime of 15s or so, rather than completely eliminating the cache.
Examples:
-
10 minutes: 600
-
one 60 minutes: 3600
-
Meet the Caching section below for detailed information on how the enshroud operates.
Directory settings
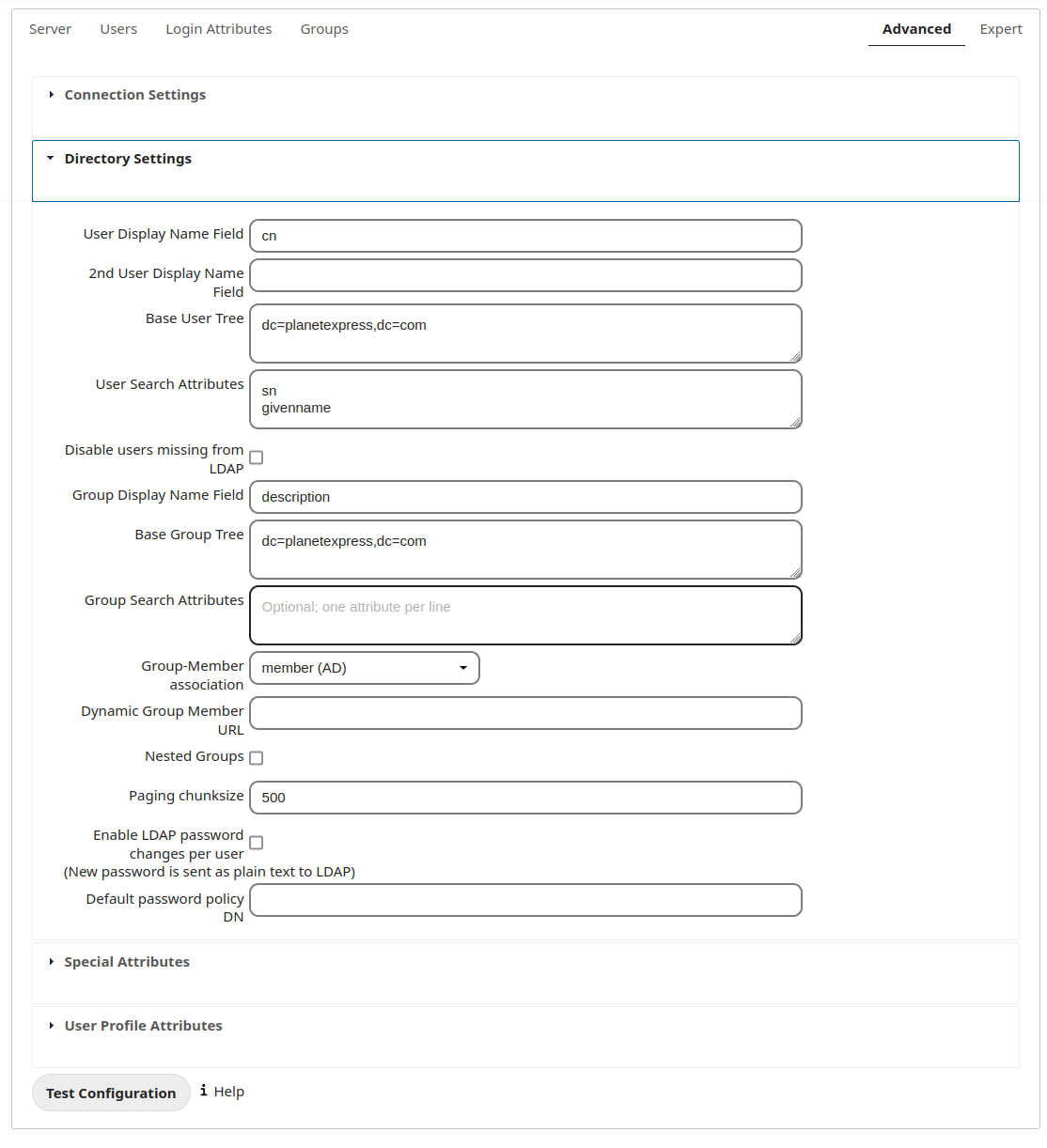
- User Display Name Field:
-
The aspect that should be used every bit brandish proper name in Nextcloud.
-
Example: displayName
-
- 2nd User Display Proper noun Field:
-
An optional second attribute displayed in brackets after the brandish proper noun, for example using the
mailaspect displays asMolly Foo (molly@example.com). - Base of operations User Tree:
-
The base DN of LDAP, from where all users tin be reached. This must be a complete DN, regardless of what you take entered for your Base DN in the Basic setting. Y'all tin can specify multiple base copse, one on each line.
-
Example:
cn=programmers,dc=my-visitor,dc=com
cn=designers,dc=my-company,dc=com
-
- User Search Attributes:
-
These attributes are used when searches for users are performed, for example in the share dialogue. The user display name attribute is the default. You lot may list multiple attributes, one per line.
If an attribute is not bachelor on a user object, the user will non be listed, and will be unable to login. This likewise affects the display name attribute. If you override the default you must specify the display name attribute hither.
-
Example:
-
- Grouping Brandish Name Field:
-
The attribute that should be used equally Nextcloud group name. Nextcloud allows a limited set of characters (a-zA-Z0-ix.-_@). One time a group name is assigned it cannot be inverse.
-
Example: cn
-
- Base Group Tree:
-
The base of operations DN of LDAP, from where all groups can exist reached. This must exist a complete DN, regardless of what you take entered for your Base DN in the Basic setting. Y'all can specify multiple base copse, i in each line.
-
Example:
cn=barcelona,dc=my-company,dc=com
cn=madrid,dc=my-company,dc=com
-
- Group Search Attributes:
-
These attributes are used when a search for groups is washed, for example in the share dialogue. By default the group display name attribute as specified in a higher place is used. Multiple attributes can be given, one in each line.
If you override the default, the group display name aspect will not be taken into account, unless you specify it as well.
-
Case:
-
- Grouping Member association:
-
The attribute that is used to indicate group memberships, i.due east. the attribute used by LDAP groups to refer to their users.
Nextcloud detects the value automatically. You should only change it if you accept a very valid reason and know what you are doing.
-
Example: uniquemember
-
- Nested groups:
-
Enable group member retrieval from sub groups.
To allow user listing and login from nested groups, please see User list and login per nested groups in the department Troubleshooting, Tips and Tricks.
- Enable LDAP password changes per user:
-
Allow LDAP users to modify their password and permit Super Administrators and Group Administrators to change the password of their LDAP users.
To enable this feature, the post-obit requirements accept to be met:
-
General requirements:
-
Access control policies must be configured on the LDAP server to grant permissions for password changes. The User DN every bit configured in Server Settings needs to have write permissions in order to update the userPassword attribute.
-
Passwords are sent in plaintext to the LDAP server. Therefore, ship encryption must be used for the advice between Nextcloud and the LDAP server, e.m. employ LDAPS.
-
Enabling password hashing on the LDAP server is highly recommended. While Active Directory stores passwords in a one-way format by default, OpenLDAP users could configure the
ppolicy_hash_cleartextdirective of the ppolicy overlay that ships with OpenLDAP.
-
Additional requirements for Active Directory:
-
At least a 128-bit transport encryption must be used for the advice betwixt Nextcloud and the LDAP server.
-
Make sure that the
fUserPwdSupportchar of the dSHeuristics is configured to employ theuserPasswordattribute asunicodePwdallonym. While this is prepare accordingly on AD LDS by default, this is non the case on Advertizement DS.
-
- Default password policy DN:
-
This feature requires OpenLDAP with ppolicy. The DN of a default password policy will be used for countersign expiry handling in the absence of whatsoever user specific password policy. Password expiry handling features the following:
-
When a LDAP countersign is well-nigh to expire, display a warning bulletin to the user showing the number of days left before it expires. Password decease warnings are displayed through the notifications app for Nextcloud.
-
Prompt LDAP users with expired passwords to reset their countersign during login, provided that an adequate number of grace logins is still bachelor.
Get out the setting empty to keep countersign expiry handling disabled.
For the password expiry handling feature to work, LDAP password changes per user must be enabled and the LDAP server must be running OpenLDAP with its ppolicy module configured accordingly.
-
Example:
cn=default,ou=policies,dc=my-company,dc=com
-
Special attributes
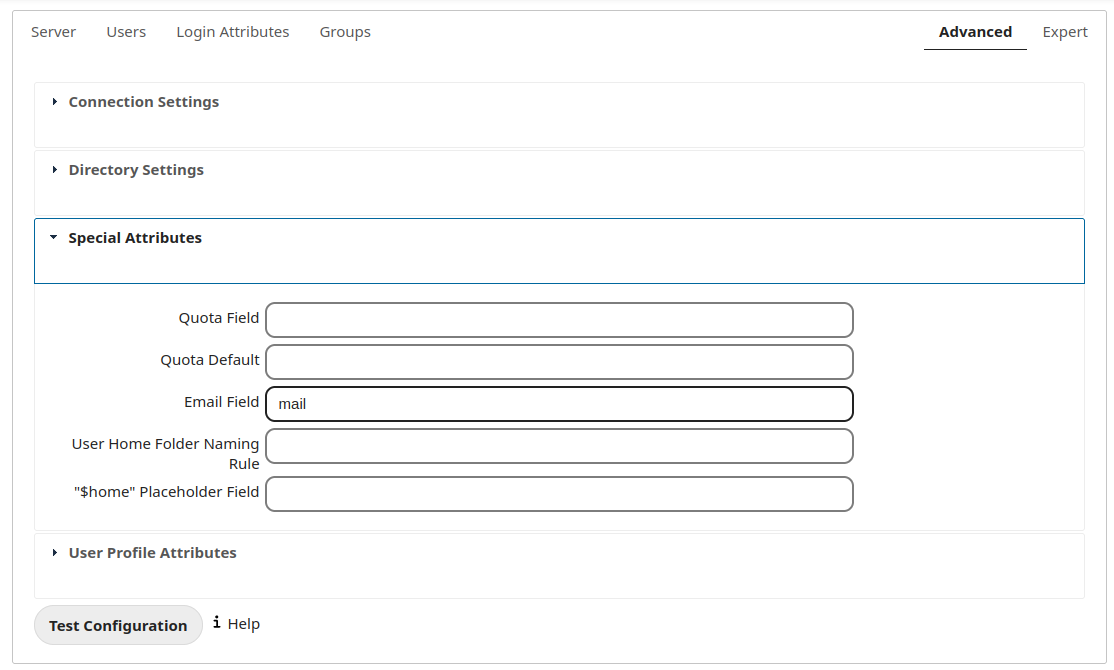
- Quota Field:
-
Nextcloud tin read an LDAP aspect and set the user quota according to its value. Specify the attribute here, and it will render human-readable values, e.m. "two GB". Any quota prepare in LDAP overrides quotas set on the Nextcloud user management page.
-
Instance: NextcloudQuota
-
- Quota Default:
-
Override Nextcloud default quota for LDAP users who exercise non have a quota gear up in the Quota Field.
-
Example: 15 GB
-
- Email Field:
-
Prepare the user's email from their LDAP attribute. Go out it empty for default behavior.
-
Case: post
-
- User Home Binder Naming Dominion:
-
Past default, the Nextcloud server creates the user directory in your Nextcloud data directory and gives it the Nextcloud username, .east.g
/var/world wide web/nextcloud/data/alice. Y'all may desire to override this setting and proper name it after an LDAP attribute value. The aspect can also render an absolute path, e.g./mnt/storage43/alice. Leave it empty for default behavior.-
Case: cn
-
In new Nextcloud installations the home folder rule is enforced. This ways that one time you set a home folder naming rule (get a habitation binder from an LDAP attribute), information technology must be available for all users. If information technology isn't available for a user, then that user volition not be able to login. Also, the filesystem volition non be set up for that user, so their file shares will non be available to other users.
In migrated Nextcloud installations the old behavior all the same applies, which is using the Nextcloud username as the dwelling binder when an LDAP aspect is not set. You may change this enforcing the home binder rule with the occ command in Nextcloud, similar this example on Ubuntu:
sudo - u www - data php occ config : app : prepare user_ldap enforce_home_folder_naming_rule -- value = one Adept settings
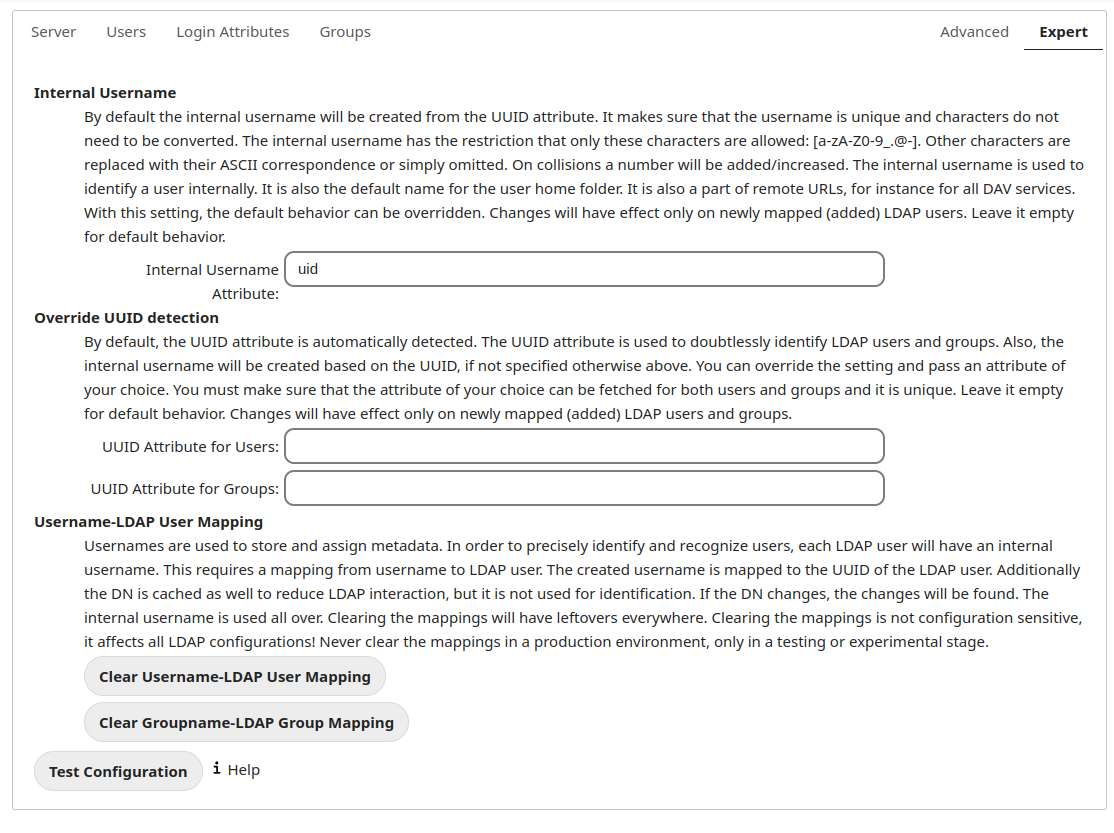
In the Proficient Settings fundamental beliefs can be adjusted to your needs. The configuration should be well-tested before starting product use.
- Internal Username:
-
The internal username is the identifier in Nextcloud for LDAP users. By default information technology will be created from the UUID aspect. The UUID attribute ensures that the username is unique, and that characters do not need to exist converted. Only these characters are allowed: [a-zA-Z0-9_.@-]. Other characters are replaced with their ASCII equivalents, or are simply omitted.
The LDAP backend ensures that in that location are no duplicate internal usernames in Nextcloud, i.east. that information technology is checking all other activated user backends (including local Nextcloud users). On collisions a random number (between m and 9999) will exist attached to the retrieved value. For example, if "alice" exists, the next username may be "alice_1337".
The internal username is the default name for the user home folder in Nextcloud. It is as well a part of remote URLs, for instance for all *DAV services.
You tin can override all of this with the Internal Username setting. Exit it empty for default behavior. Changes will bear on but newly mapped LDAP users.
When configuring this, exist aware that the username in Nextcloud is considered immutable and cannot be changed afterwards. This tin can cause issues when using an attribute that might change, e.yard. the e-mail address of a user that will go inverse during name alter.
-
Case: uid
-
- Override UUID detection
-
By default, Nextcloud motorcar-detects the UUID attribute. The UUID attribute is used to uniquely identify LDAP users and groups. The internal username volition be created based on the UUID, if not specified otherwise.
You tin can override the setting and pass an attribute of your pick. You must brand sure that the attribute of your pick tin exist fetched for both users and groups and it is unique. Exit it empty for default behavior. Changes will accept effect only on newly mapped LDAP users and groups. It also will take effect when a user's or grouping's DN changes and an one-time UUID was cached, which will result in a new user. Because of this, the setting should be applied earlier putting Nextcloud in production employ and clearing the bindings (run into the
User and Grouping Mappingdepartment below).-
Case: cn
-
- Username-LDAP User Mapping
-
Nextcloud uses usernames equally keys to store and assign data. In society to precisely identify and recognize users, each LDAP user will take a internal username in Nextcloud. This requires a mapping from Nextcloud username to LDAP user. The created username is mapped to the UUID of the LDAP user. Additionally the DN is cached likewise to reduce LDAP interaction, but it is not used for identification. If the DN changes, the alter volition be detected by Nextcloud by checking the UUID value.
The same is valid for groups.
The internal Nextcloud name is used all over in Nextcloud. Clearing the Mappings will take leftovers everywhere. Never articulate the mappings in a production surroundings, but only in a testing or experimental server.
Warning
Immigration the Mappings is not configuration sensitive, it affects all LDAP configurations!
Testing the configuration
The Test Configuration push checks the values every bit currently given in the input fields. You do non need to save earlier testing. By clicking on the push, Nextcloud will try to bind to the Nextcloud server using the settings currently given in the input fields. If the binding fails you'll see a yellow banner with the fault message "The configuration is invalid. Please have a wait at the logs for further details."
When the configuration examination reports success, relieve your settings and check if the users and groups are fetched correctly on the Users folio.
Additional configuration options via occ
Few configuration settings can simply be set on control line via occ .
Attribute update interval
The LDAP backend will update user information that is used inside Nextcloud with the values provided by the LDAP server. For example these are electronic mail, quota or the avatar. This happens on every login, the first detection of a user from LDAP and regularly by a background task.
The interval value determines the fourth dimension between updates of the values and is used to avoid frequent overhead, including time-expensive write actions to the database.
The interval is described in seconds and it defaults to 86400 equalling a day. Information technology is non a per-configuration pick.
The value tin be modified past:
sudo - u www - data php occ config : app : set user_ldap updateAttributesInterval -- value = 86400 A value of 0 volition update it on every of the named occasions.
Nextcloud avatar integration
Nextcloud supports user profile pictures, which are as well chosen avatars. If a user has a photo stored in the jpegPhoto or thumbnailPhoto attribute on your LDAP server, information technology volition be used every bit their avatar. In this case the user cannot modify their avatar (on their Personal page) equally it must exist changed in LDAP. jpegPhoto is preferred over thumbnailPhoto.
If the jpegPhoto or thumbnailPhoto attribute is not set or empty, then users can upload and manage their avatars on their Nextcloud Personal pages. Avatars managed in Nextcloud are not stored in LDAP.
The jpegPhoto or thumbnailPhoto aspect is fetched one time a day to brand sure the current photo from LDAP is used in Nextcloud. LDAP avatars override Nextcloud avatars, and when an LDAP avatar is deleted then the near recent Nextcloud avatar replaces information technology.
Photos served from LDAP are automatically cropped and resized in Nextcloud. This affects just the presentation, and the original image is not changed.
Use a specific aspect or turn off loading of images
It is possible to plough off the avatar integration or specify a single, different aspect to read the image from. It is expected to contain image data just like jpegPhoto or thumbnailPhoto exercise.
The behaviour tin be changed using the occ command line tool only. Essentially those options are bachelor:
-
The default behaviour equally described above should be used
occ ldap:set-config "s01" "ldapUserAvatarRule" "default" -
User images shall not be fetched from LDAP
occ ldap:set-config "s01" "ldapUserAvatarRule" "none" -
The paradigm should be read from the attribute "selfiePhoto"
occ ldap:ready-config "s01" "ldapUserAvatarRule" "data:selfiePhoto"
The "s01" refers to the configuration ID equally can be retrieved per occ ldap:show-config .
Troubleshooting, tips and tricks
SSL certificate verification (LDAPS, TLS)
A common error with SSL certificates is that they may not exist known to PHP. If you lot have trouble with certificate validation make certain that
-
You lot have the certificate of the server installed on the Nextcloud server
-
The certificate is appear in the system's LDAP configuration file (usually /etc/ldap/ldap.conf)
-
Using LDAPS, likewise brand sure that the port is correctly configured (by default 636)
Microsoft Active Directory
Compared to earlier Nextcloud versions, no further tweaks need to be done to make Nextcloud piece of work with Active Directory. Nextcloud will automatically find the right configuration in the fix-upwardly procedure.
memberOf / read memberof permissions
If you lot want to use memberOf within your filter y'all might need to give your querying user the permissions to employ it. For Microsoft Agile Directory this is described here.
User listing and login per nested groups
When information technology is intended to allow user listing and login based on a specific group having subgroups ("nested groups"), checking Nested groups on Directory Settings is not enough. Also the User (and Login) filter demand to exist changed, by specifying the LDAP_MATCHING_RULE_IN_CHAIN matching rule. Change the filter parts containing the memberof condition according to this case:
(memberof=cn=Nextcloud Users Group,ou=Groups,…)
to
(memberof:1.two.840.113556.1.iv.1941:=cn=Nextcloud Users Group,ou=Groups,…)
Duplicating server configurations
In case y'all have a working configuration and want to create a similar 1 or "snapshot" configurations before modifying them y'all tin do the following:
-
Go to the Server tab
-
On Server Configuration cull Add together Server Configuration
-
Answer the question Take over settings from recent server configuration? with yep.
-
(optional) Switch to Avant-garde tab and uncheck Configuration Agile in the Connection Settings, so the new configuration is non used on Save
-
Click on Relieve
Now y'all can change and enable the configuration.
Nextcloud LDAP internals
Some parts of how the LDAP backend works are described here.
User and grouping mapping
In Nextcloud the user or group name is used to have all relevant information in the database assigned. To work reliably a permanent internal user name and group proper name is created and mapped to the LDAP DN and UUID. If the DN changes in LDAP it volition exist detected, and there volition exist no conflicts.
Those mappings are done in the database tabular array ldap_user_mapping and ldap_group_mapping . The user name is likewise used for the user'south folder (except if something else is specified in User Home Binder Naming Dominion), which contains files and meta data.
The internal user name and a visible display name are separated. This is non the example for group names, yet, i.e. a grouping name cannot be altered.
That means that your LDAP configuration should be skilful and set before putting it into product. The mapping tables are filled early on, just every bit long as y'all are testing, yous can empty the tables any time. Do not do this in production.
The attributes of users are fetched on demand (i.due east. for sharing autocompletion or in the user management) and and then stored inside the Nextcloud database to allow a amend functioning on our side. They are typically checked twice a mean solar day in batches from all users again. Beside that they are also refreshed during a login for this user or tin be fetched manually via the occ command occ ldap:check-user --update USERID where USERID is Nextcloud's user id.
Caching
The LDAP information is cached in Nextcloud retentiveness enshroud, and you must install and configure the memory cache (encounter Retention caching). The Nextcloud Enshroud helps to speed upward user interactions and sharing. It is populated on need, and remains populated until the Cache Time-To-Live for each unique request expires. User logins are non cached, so if yous need to meliorate login times fix a slave LDAP server to share the load.
You tin arrange the Enshroud Time-To-Alive value to balance performance and freshness of LDAP data. All LDAP requests will be cached for 10 minutes past default, and y'all tin alter this with the Cache Time-To-Live setting. The cache answers each request that is identical to a previous request, within the fourth dimension-to-live of the original asking, rather than striking the LDAP server.
The Cache Time-To-Alive is related to each single asking. Later on a cache entry expires there is no automatic trigger for re-populating the information, as the cache is populated only by new requests, for example by opening the User administration folio, or searching in a sharing dialog.
There is 1 trigger which is automatically triggered by a sure background job which keeps the user-grouping-mappings up-to-date, and always in cache.
Nether normal circumstances, all users are never loaded at the same time. Typically the loading of users happens while page results are generated, in steps of 30 until the limit is reached or no results are left. For this to work on a Nextcloud-Server and LDAP-Server, Paged Results must exist supported.
Nextcloud remembers which user belongs to which LDAP-configuration. That means each request volition always be directed to the correct server unless a user is defunct, for example due to a server migration or unreachable server. In this case the other servers will also receive the asking.
Handling with fill-in server
When Nextcloud is not able to contact the main LDAP server, Nextcloud assumes information technology is offline and will not try to connect again for the fourth dimension specified in Enshroud Time-To-Live. If you have a fill-in server configured Nextcloud volition connect to it instead. When you lot have scheduled downtime, check Disable Main Server to avoid unnecessary connection attempts.
Note
When a LDAP object's name or surname, that is display name attribute, by default "displayname", is left empty, Nextcloud will treat information technology as an empty object, therefore no results from this user or AD-Object will be shown to avoid gathering of technical accounts.
Source: https://docs.nextcloud.com/server/latest/admin_manual/configuration_user/user_auth_ldap.html
0 Response to "Nextcloud Client Wont Connect Error Reads Ldap Server"
Post a Comment